Módulos opcionales de Weblate¶
Hay varios módulos opcionales disponibles para que los configure.
Git exporter¶
Nuevo en la versión 2.10.
Provides you read-only access to the underlying Git repository using HTTP(S).
Instalación¶
Add
weblate.gitexportto installed apps insettings.py:
INSTALLED_APPS += ("weblate.gitexport",)
Export existing repositories by migrating your database after installation:
weblate migrate
Uso¶
The module automatically hooks into Weblate and sets the exported repository URL in
the Configuración de componentes.
The repositories are accessible under the /git/ part of the Weblate URL, for example
https://example.org/git/weblate/main/.
Repositories for publicly available projects can be cloned without authentication:
git clone 'https://example.org/git/weblate/main/'
Access to browse the repositories with restricted access (with Private
access control or when REQUIRE_LOGIN is enabled)
requires an API token which can be obtained in your
user profile:
git clone 'https://user:KEY@example.org/git/weblate/main/'
Consejo
By default members or Users group and anonymous user have access to the repositories for public projects via Access repository and Power user roles.
Facturación¶
Nuevo en la versión 2.4.
This is used on Hosted Weblate to define billing plans, track invoices and usage limits.
Instalación¶
1. Add weblate.billing to installed apps in
settings.py:
INSTALLED_APPS += ("weblate.billing",)
Run the database migration to optionally install additional database structures for the module:
weblate migrate
Uso¶
After installation you can control billing in the admin interface. Users with billing enabled will get new Billing tab in their Perfil de usuario.
The billing module additionally allows project admins to create new projects and components without being superusers (see Añadir proyectos y componentes de traducción). This is possible when following conditions are met:
The billing is in its configured limits (any overusage results in blocking of project/component creation) and paid (if its price is non zero)
The user is admin of existing project with billing or user is owner of billing (the latter is necessary when creating new billing for users to be able to import new projects).
Upon project creation user is able to choose which billing should be charged for the project in case he has access to more of them.
Información legal¶
Nuevo en la versión 2.15.
This is used on Hosted Weblate to provide required legal documents. It comes provided with blank documents, and you are expected to fill out the following templates in the documents:
legal/documents/tos.htmlTerms of service document
legal/documents/privacy.htmlPrivacy policy document
legal/documents/summary.htmlShort overview of the terms of service and privacy policy
Nota
Legal documents for the Hosted Weblate service are available in this Git repository <https://github.com/WeblateOrg/wllegal/tree/main/wllegal/templates/legal/documents>.
Most likely these will not be directly usable to you, but might come in handy as a starting point if adjusted to meet your needs.
Instalación¶
1. Add weblate.legal to installed apps in
settings.py:
INSTALLED_APPS += ("weblate.legal",)
# Optional:
# Social auth pipeline to confirm TOS upon registration/subsequent sign in
SOCIAL_AUTH_PIPELINE += ("weblate.legal.pipeline.tos_confirm",)
# Middleware to enforce TOS confirmation of signed in users
MIDDLEWARE += [
"weblate.legal.middleware.RequireTOSMiddleware",
]
Run the database migration to optionally install additional database structures for the module:
weblate migrate
Edit the legal documents in the
weblate/legal/templates/legal/folder to match your service.
Uso¶
After installation and editing, the legal documents are shown in the Weblate UI.
Avatars¶
Avatars are downloaded and cached server-side to reduce information leaks to the sites serving them
by default. The built-in support for fetching avatars from e-mails addresses configured for it can be
turned off using ENABLE_AVATARS.
Weblate currently supports:
Ver también
Spam protection¶
You can protect against spamming by users by using the Akismet service.
Install the akismet Python module (this is already included in the official Docker image).
Obtain the Akismet API key.
Store it as
AKISMET_API_KEYorWEBLATE_AKISMET_API_KEYin Docker.
Following content is sent to Akismet for checking:
Suggestions from unauthenticated users
Project and component descriptions and links
Nota
This (among other things) relies on IP address of the client, please see Running behind reverse proxy for properly configuring that.
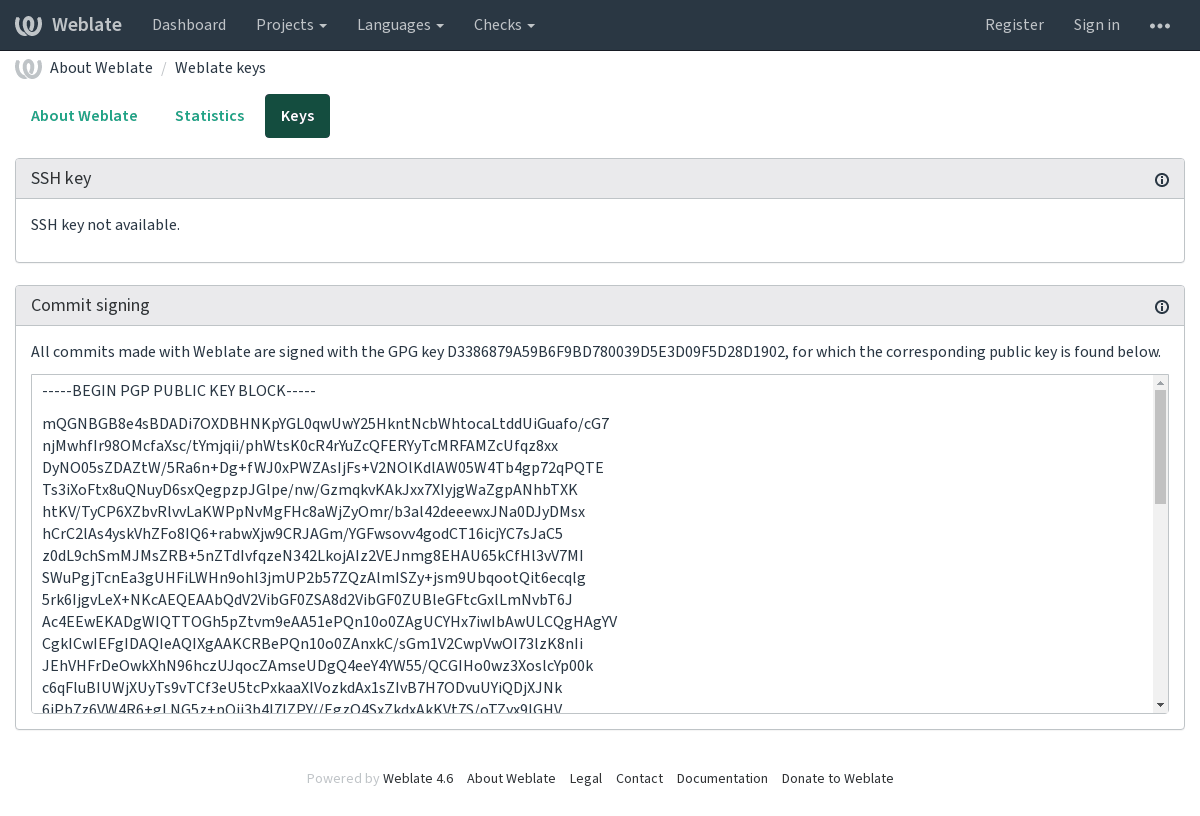
Signing Git commits with GnuPG¶
Nuevo en la versión 3.1.
All commits can be signed by the GnuPG key of the Weblate instance.
1. Turn on WEBLATE_GPG_IDENTITY. (Weblate will generate a GnuPG
key when needed and will use it to sign all translation commits.)
This feature needs GnuPG 2.1 or newer installed.
You can find the key in the DATA_DIR and the public key is shown on
the «About» page:
2. Alternatively you can also import existing keys into Weblate, just set
HOME=$DATA_DIR/home when invoking gpg.
Ver también
Rate limiting¶
Distinto en la versión 3.2: The rate limiting now accepts more fine-grained configuration.
Distinto en la versión 4.6: The rate limiting no longer applies to superusers.
Several operations in Weblate are rate limited. At most
RATELIMIT_ATTEMPTS attempts are allowed within RATELIMIT_WINDOW seconds.
The user is then blocked for RATELIMIT_LOCKOUT. There are also settings specific to scopes, for example RATELIMIT_CONTACT_ATTEMPTS or RATELIMIT_TRANSLATE_ATTEMPTS. The table below is a full list of available scopes.
The following operations are subject to rate limiting:
Nombre |
Alcance |
Intentos permitidos |
Oportunidad del límite de velocidad |
Período de bloqueo |
|---|---|---|---|---|
Registro |
|
5 |
300 |
600 |
Enviar un mensaje a los administradores |
|
5 |
300 |
600 |
Password authentication on sign in |
|
5 |
300 |
600 |
Búsqueda en todo el sitio |
|
6 |
60 |
60 |
Traducción |
|
30 |
60 |
600 |
Adición al glosario |
|
30 |
60 |
600 |
Comenzar una traducción en un idioma nuevo |
|
2 |
300 |
600 |
If a user fails to log in AUTH_LOCK_ATTEMPTS times, password authentication will be turned off on the account until having gone through the process of having its password reset.
The settings can be also applied in the Docker container by adding WEBLATE_ prefix to the setting name, for example RATELIMIT_ATTEMPTS becomes WEBLATE_RATELIMIT_ATTEMPTS.
The API has separate rate limiting settings, see API rate limiting.
Ver también
Rate limiting, Running behind reverse proxy, API rate limiting
Integración con Fedora Messaging¶
Fedora Messaging es un publicador basado en AMQP para todos los cambios que ocurren en Weblate. Puede integrar servicios adicionales para actuar ante cambios que ocurran en Weblate mediante esta herramienta.
La integración con Fedora Messaging está disponible como un módulo Python separado, weblate-fedora-messaging. Consulte <https://github.com/WeblateOrg/fedora_messaging/> para obtener instrucciones de instalación.